Guide for OpenID+WebID? Proxy Service that Enables WebID? Exploitation via OpenID
What?
Virtuoso OpenID+WebID? Proxy Service.Why?
All of our early WebID? demonstrations focused on exposing the critical value that WebID? brings to OpenID. Basically, that takes the form of eliminating username-and-password-based authentication on the more obvious front, while disambiguating hyperlink-based Names and Addresses on the less obvious front, with Linked Data in mind (i.e., via OpenID you ended up with a URI based global Identifier with the requisite fidelity for InterWeb? scale User Centric Identity)In recent times, we've decoupled many of our WebID? implementation layers from both Virtuoso and ODS. The net effects of these actions are:
- HTML-, Windows-, and iOS5-based X.509 certificate generators that deliver certificates bearing WebID? watermarks -- http://id.myopenlink.net/certgen/
- HTML-based WebID? verifier that enables you quickly verify any WebID? -- http://id.myopenlink.net/ods/webid_demo.html
- OpenID+WebID? proxy service than enables WebID? exploitation via OpenID
How?
What follows is a simple step-by guide showcasing the OpenID+WebID? proxy service:
- Get yourself a WebID.
- Visit a space on the InterWeb? that supports OpenID-based authentication.
- When challenged for your WebID? URL, simply provide a URL in the following form:
http://id.myopenlink.net/openid-proxy/id.vsp?w={Your-WebID}- For instance, Kingsley Idehen's OpenID's is http://id.myopenlink.net/dataspace/person/KingsleyUyiIdehen and Kingsley Idehen's WebID?'s is http://id.myopenlink.net/dataspace/person/KingsleyUyiIdehen#this, so the provided URL could be:
http://id.myopenlink.net/openid-proxy/id.vsp?w=http://id.myopenlink.net/dataspace/person/KingsleyUyiIdehen#this
- For instance, Kingsley Idehen's OpenID's is http://id.myopenlink.net/dataspace/person/KingsleyUyiIdehen and Kingsley Idehen's WebID?'s is http://id.myopenlink.net/dataspace/person/KingsleyUyiIdehen#this, so the provided URL could be:
Observations
You will notice that you are able to use OpenID without username-and-password-based authentication. You simply present your X.509 certificate, and that's it.
Why is this important?
WebID? is best understood and appreciated when experienced as a complementary enhancement of what exists.
Here is a sequence of screenshots that showcase OpenID+WebID? using the decoupled proxy service we now provide, distinct from the ODS instances used in our much earlier implementation demos:
Example
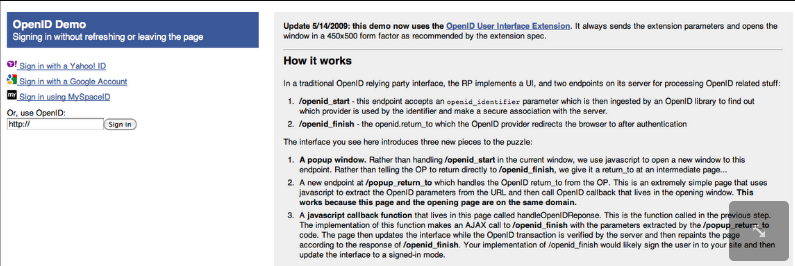
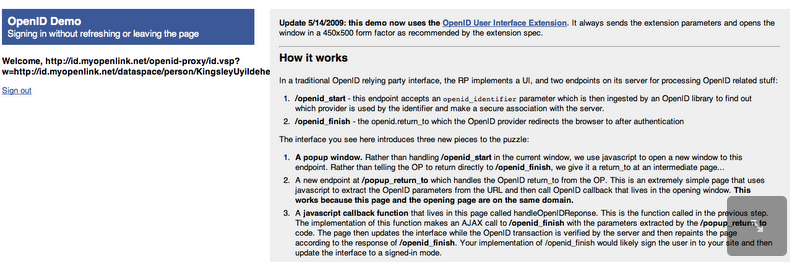
- Load http://openid-demo.appspot.com/ in your web browser.
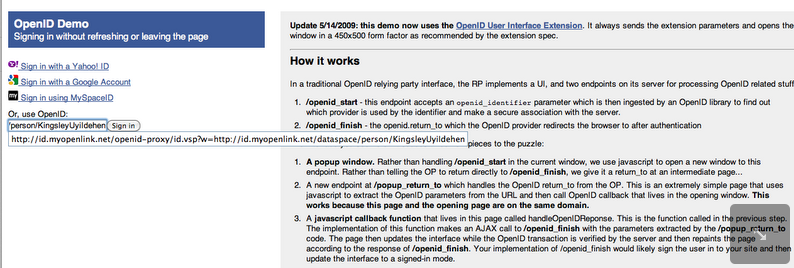
- Enter your WebID?:
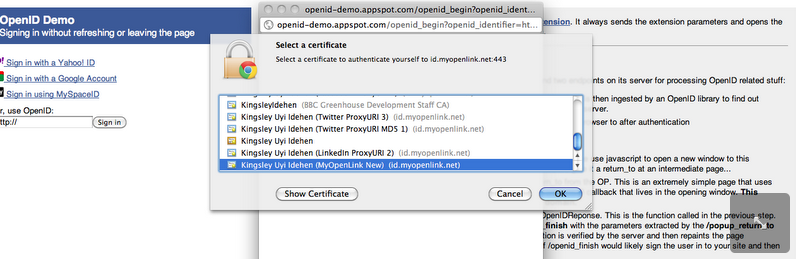
- When challenged for certificate authorization, select your X.509 certificate:
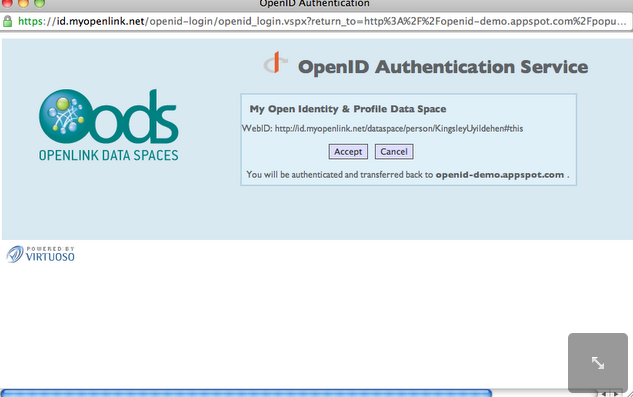
- You should be redirected to Virtuoso OpenID Authentication Service Endpoint, asking you how to proceed further.
Click Accept:
- Finally, you should be successfully logged in:
Related
- Power of WebID + OpenID Hybrid Protocol via Internet Explorer & Windows
- Using Safari to Demonstrate WebID + OpenID Hybrid Protocol Power!
- Using Virtuoso's WebID Verification Proxy Service with a WebID-bearing X.509 certificate
- Using Virtuoso's WebID Identity Provider (IdP) Proxy Service with an X.509 certificate
- WebID Protocol & SPARQL Endpoint ACLs Tutorial
- Safeguarding your Virtuoso-hosted SPARQL Endpoint
- SPARQL Endpoint Protection Methods Collection
- Virtuoso documentation
- Virtuoso Tips and Tricks Collection
- SPARUL over SPARQL using the http://cname:port/sparql-auth endpoint
- Virtuoso Authentication Server UI
- Manage a SPARQL-WebID based Endpoint
- Configure Virtuoso instance as an X.509 Certificate Authority and HTTPS listener
- Configure Virtuoso+ODS instance as an X.509 Certificate Authority and HTTPS listener
- WebID Protocol Support in OpenLink Data Spaces.
- Manage ODS Datadspaces Objects WebID? Access Control Lists (ACLs):
- Guide for Set up a X.509 certificate issuer and HTTPS listener and generate ODS user certificates.
- Setting up PubSubHub in ODS
- PubSubHubBub Demo Client Example
- Feed subscription via PubSubHub protocol Example
- Setting Up PubSubHub to use WebID Protocol or IP based control lists
- CA Keys Import using Conductor
- Generate an X.509 Certificate hosted WebID Guide
- Generate an X.509 Certificate (with a WebID watermark) to be managed by host operating system keystore
- Generate an X.509 Certificate (with a WebID watermark) to be managed by a browser-based keystore
- ODS Briefcase WebID Protocol Share File Guide
- WebID Protocol Specification
- Test WebID Protocol Certificate page
- WebID Protocol Certificate Generation page
- openid4.me -- An early WebID?+OpenID implementation that isn't currently functional, but still provides good insights into the inner workings of WebID?+OpenID
- A nice OpenID service for testing the prowess of OpenID+WebID
- An WebID?+OpenID protocol demo using ODS ...
- Using WebID from an iOS5 device (iPhone or iPad) with Twitter as the Identity Provider (IdP) service